Read translated versions of the report in Arabic, Brazilian Portuguese, French, German, Hindi, Indonesian, Korean, Serbo Croatian, Spanish, Turkish, and Vietnamese.
Executive Summary
In late 2018, amid American concerns about whether Canada would welcome Huawei into its telecommunications networks, Canadian Prime Minister Justin Trudeau made a series of statements that captured conventional wisdom across much of the world. “It shouldn’t be a political decision,” he declared at the time, and Canada would not “let politics slip into decisions” about Huawei’s role in its network.1
The notion that power politics could be removed from questions over telecommunications was not only optimistic, it was also out of step with the history of telecommunications. This report explores that history, and it shows how power and telecommunications have almost always been closely linked. When states ignored those linkages and were cavalier with the security of their own networks, the results were disadvantageous and at times even disastrous.
This report examines several major cases of great power competition in telecommunications dating back to the earliest inception of electrical telecommunications in the 1840s. These cases demonstrate that many of the questions policymakers confront today have close analogues to the past. While the present debate over network security and 5G infrastructure may feel new, it in fact echoes forgotten disputes dating back to the dawn of electrical telecommunications some 150 years ago. Moreover, many of the familiar elements of telecommunications competition today — such as the use of standard-setting bodies, state subsidies, cable taps, information warfare, developing country markets, and encryption to gain advantage — were developed more than a century ago, with important lessons for present debates.
A list of these key lessons is provided below:
1
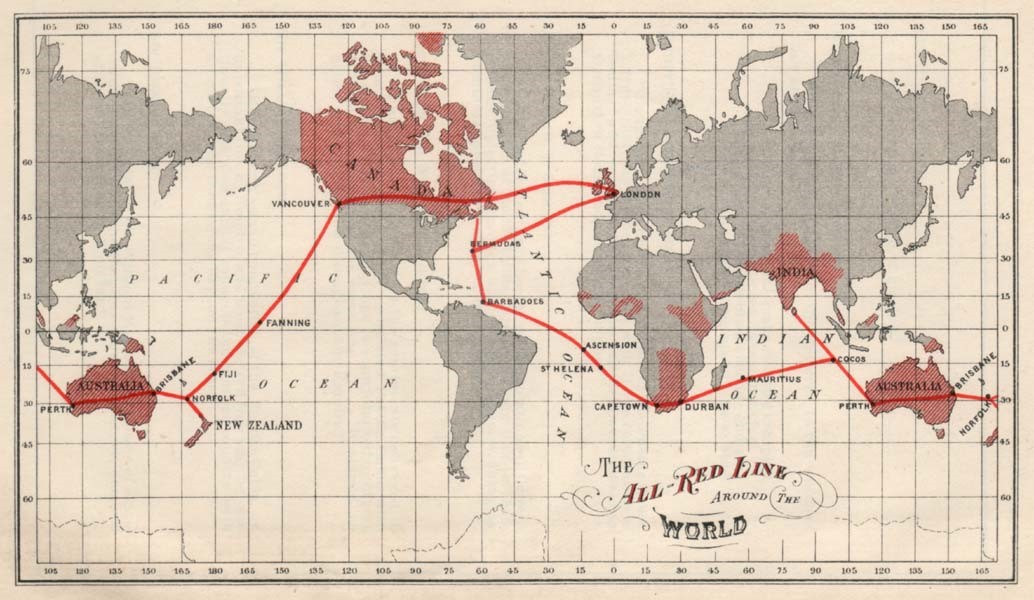
Control over global telecommunications networks is a form of political power. 5G networks are expected to form the foundation of a smarter, connected economy linking countless devices and sensors together. Eager to build these networks worldwide, China has subsidized its 5G champion companies and projects around the world as part of a “Digital Silk Road” initiative. That effort is analogous to Great Britain’s pursuit of network dominance at the dawn of electrical telegraphy. Britain built its advantage over six decades by steadily increasing the dependence of other states on its networks — even forgoing fees and economic benefits to entice them to run cables through Britain — while also reducing Britain’s dependence on foreign networks. It eventually controlled more than half of the world’s cable traffic, the largest radio network, and the largest fleet of cable ships. Britain’s “information hegemony” allowed it to cut Germany off from virtually all global telecommunications in World War I and forced Berlin to route traffic over British-owned lines susceptible to British monitoring, which later proved decisive in Germany’s defeat in the conflict.
2
Long periods of peace and prosperity generally lead to complacency about telecommunications risks. In the last 30 years, post-Cold War peace and economic globalization coincided with rapid progress in telecommunications that led states to prioritize revolutionary commercial benefits over political and security risks, including even foreign ownership or operation of networks. A similar development took place at the dawn of telecommunications in the 1840s, which also coincided with a period of relative peace and globalization that continued until World War I. For much of that era, the desire to capture the seemingly miraculous commercial potential of new communications technologies obscured questions related to reliance on foreign networks or companies. Great Britain benefited from the complacency of others by building and then exploiting an unassailable nodal position in global networks, with most other great powers dependent on its networks.
3
When states are complacent about their telecommunications security, the results can be disastrous and reshape world politics. Decades of German complacency about its dependence on British telecommunications lines meant that by the time Berlin awakened to the risks of that dependency, it was too late to change it. When World War I broke out, Britain cut all of Germany’s cables and forced Berlin to route traffic through British networks despite the risk of interception, which led to the uncovering of the “Zimmerman telegram,” which helped bring the United States into the war. Similarly, Russian indiscipline in wireless radio transmissions in World War I allowed the Germans to intercept communications, “see” the movement of Russian troops in real time, and deal them a decisive defeat at the Battle of Tannenberg. Then, in World War II, Nazi overconfidence in its ciphers led to minimal efforts to update them, allowing Great Britain to break the codes and obtain intelligence that is believed to have shortened the war by two to four years. Given the power of information, even occasional bouts of signals indiscipline or complacency can alter history.
4
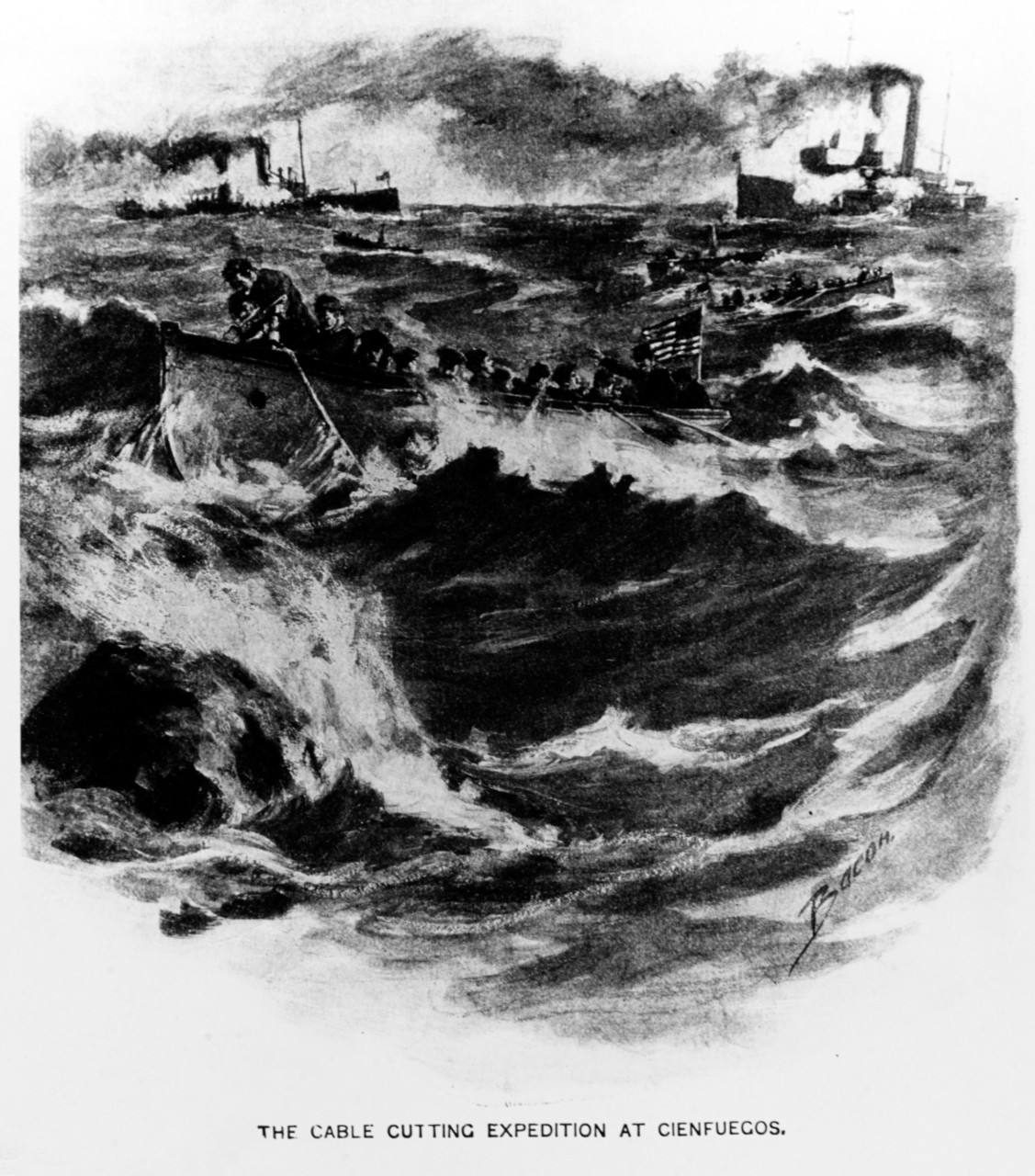
New technology always leads to new efforts to intercept it. The emergence of undersea cables led to efforts to cut and tap those lines as early as the Spanish-American War; radio transmission gave rise to efforts by rivals to capture network nodes and to intercept transmissions; and the emergence of sophisticated ciphers for encryption produced industrial-scale efforts to break them. In each era, some believed a new leap in communications might be less vulnerable than the ones that preceded it. Each time, however, the cycle of innovation and exploitation continued.
5
Telecommunications networks have never been politically neutral, particularly in times of tension. In 2019, Huawei executives made a “no-backdoor, no-spying” pledge and promised that their company would remain outside of politics, with China’s government committing to respect the pledge. But even more than a century ago, telecommunications companies and their host governments made similar promises publicly while privately breaking them and working together in both peacetime and wartime. For example, British dominance in undersea cables led the French, Germans, and Americans to advocate for keeping the lines neutral, even in war. British firms publicly declared their neutrality but in actuality deferred to British political interests, particularly at moments of great tension, and gave up neutrality entirely during periods of war. The power that comes from disrupting or intercepting rival information flows has generally been too alluring for even sincere claims of neutrality to endure.
6
States often seek their own telecommunications champions once they recognize the vulnerability of relying on a competitor or adversary’s firms. The United States currently lacks a major manufacturer of 5G base stations, which has prompted debates about whether it should invest in its own companies or rely on allied companies. It has also spurred disagreement over to what degree Huawei is itself a de facto state champion. These debates have some precedent. In the early 20th century, many states reliant on others for telecommunications equipment or networks began to build their own systems. For example, Germany pushed two German companies with competing radio efforts —Siemens & Halske and AEG — together to establish a German alternative to British dominance in radio. Many other leading states backed companies that, while ostensibly private, were intertwined with the states that supported them.
7
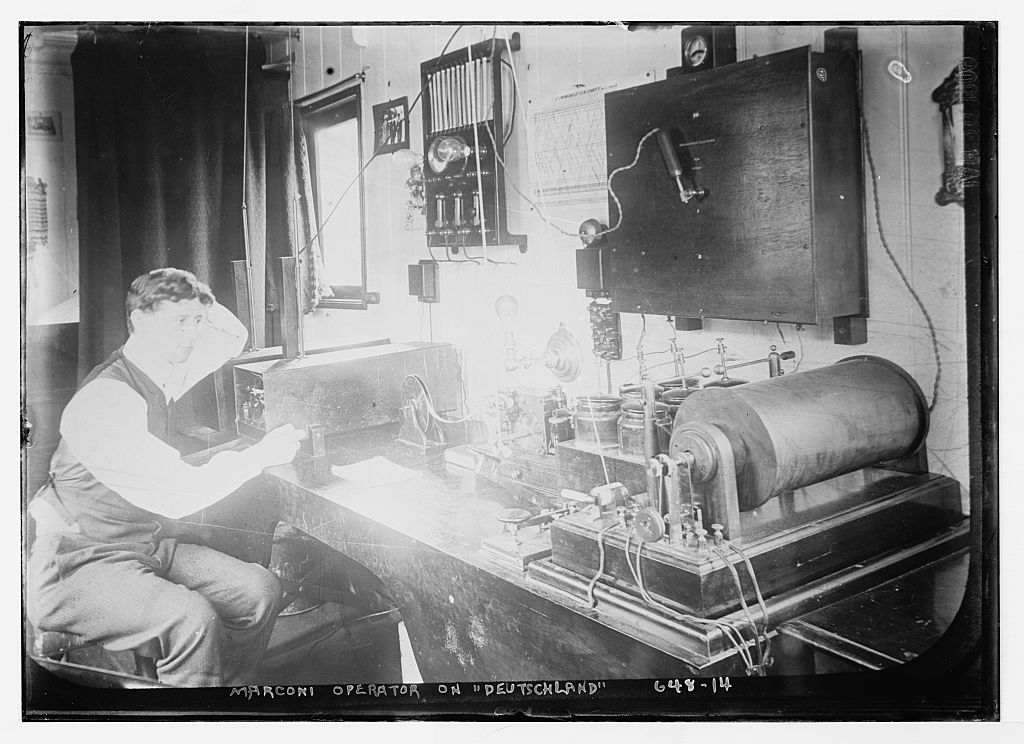
The struggle for telecommunications standards can determine which states will wield network power, and it often requires enlisting allies and partners. States whose technology becomes the dominant standard can wield that leverage over others. The current contest over information communication technology standards is, in this way, similar to the Anglo-German contest over radio networks. Britain, through the Marconi Company which it supported, was so dominant in wireless radio that all other great powers had to pass messages through Britain’s wireless network, which refused to engage with any other wireless stations. Germany ultimately found success breaking that dominance at a standard-setting body that prohibited this “non-intercommunication” policy with the help of other powers, including the United States and France — a demonstration of how similar coalitional approaches today could be used by liberal states to set or preserve favorable information and communications technology (ICT) standards if they work together.
8
States turn to encryption as their communications become easier to intercept, but encryption often has limits due to determined adversaries or user error. Some argue that anxieties over Huawei’s role in networks or over the general vulnerability of devices connected to the internet is ameliorated by modern encryption. These kinds of arguments have a long history. At the dawn of telecommunications a century ago, the possibility that telegraph messages could be read by others who controlled network nodes, or that radio could be intercepted by passive listening equipment, led to major encryption advances that bred occasional overconfidence. Germany’s complex rotor cipher machines were believed to be unbreakable, but user error and British industrial-scale efforts allowed Great Britain to compromise German codes. Low-cost updates to German equipment and ciphers could have ended Britain’s advantage, but Berlin’s overconfidence in its encryption forestalled those alterations, yielding intercepted intelligence that reshaped the course of the war. End-to-end encryption is significantly more advanced than prior efforts at encryption, but history suggests some humility is necessary.
9
Many states discount the degree to which an adversary may make extraordinary efforts to compromise their networks. Amid debates over modern telecommunications, it is worth noting that states that prioritized convenience or commerce, and therefore took security shortcuts, have often been unpleasantly surprised by the efforts a determined adversary will make to compromise their networks. In World War I, Germany was surprised by the speed and ruthlessness with which Britain cut all the cables Germany used to access the outside world; similarly, Russian commanders were surprised when their radio indiscipline led to a disastrous defeat at Tannenberg. In World War II, Germany did not expect the British to build a highly-centralized, industrial-scale code-breaking operation that could exploit German communications errors — no matter how trivial or fleeting — to break German codes. And during the Cold War, the Soviets never encrypted an internal underwater telephone line they believed was outside the reach of the United States, but Washington nonetheless found a way to tap it — gaining an invaluable source of intelligence.
10
Network security is not only about interception, but also about denial. Some of the debate over Huawei’s role in networks emphasizes questions of data security but could benefit from greater consideration of network denial, which has been an important part of great power telecommunications competition. The dawn of telegraphy saw great powers seek to cut cables and deny communications, culminating in Great Britain’s unprecedented and well-planned operation to sever all of the cables around the world that could connect Germany to the outside. Sometimes, a state may harm itself in pursuing network denial strategies, but will nonetheless proceed if it believes the harm is greater to its opponent.
العربية
إن فكرة إمكانية فصل سياسات القوى عن التساؤلات حول الاتصالات السلكية واللاسلكية ليست تفاؤلية فحسب، بل إنها أيضًا خارج إطار التاريخ. ويبين هذا التقرير أنه عندما تكون الدول غير مبالية بأمن اتصالاتها السلكية واللاسلكية، فإن النتائج قد تعيد تشكيل السياسة العالمية.
Português do Brasil
A noção de que a política das potências poderia ser excluída das questões sobre telecomunicações não é apenas otimista, mas também está em descompasso com a história das telecomunicações. Este relatório demonstra que, quando os países são negligentes com a segurança das telecomunicações, os resultados podem remodelar a política mundial.
Faça download do relatório completo (PDF) »
Français
L’idée que la politique de pouvoir puisse être éliminée des questions relatives aux télécommunications est non seulement optimiste, mais également en décalage avec l’histoire. Ce rapport montre que lorsque les États sont négligents quant à la sécurité de leurs télécommunications, les résultats peuvent redéfinir la politique mondiale.
Télécharger le rapport complet (PDF) »
Deutsch
Die Vorstellung, Telekommunikation und Machtpolitik ließen sich entkoppeln, ist nicht nur optimistisch, sondern auch geschichtsvergessen. Dieser Bericht zeigt: Wenn Staaten bei der Telekommunikationssicherheit lasch sind, können die Konsequenzen die Weltpolitik umschreiben.
Vollständigen Bericht herunterladen (PDF) »
हिन्दी
यह धारणा कि दूरसंचार पर सवाल खड़े करके सत्ता की राजनीति का खात्मा किया जा सकता है, न केवल आशावादी है बल्कि इतिहास की सोच से अलग भी है. यह रिपोर्ट बताती है कि जब राज्य अपनी दूरसंचार सुरक्षा के बारे में शालीन होते हैं, तो परिणाम विश्व राजनीति को नया रूप दे सकते हैं।
पूर्ण रिपोर्ट डाउनलोड करें (PDF) »
Bahasa Indonesia
Gagasan bahwa politik kekuasaan dapat dihilangkan dari persoalan telekomunikasi bukan hanya gagasan yang optimistis, tetapi juga tidak sejalan dengan sejarah. Laporan ini menunjukkan bahwa ketika negara merasa puas dengan keamanan telekomunikasi mereka, hasilnya dapat mengubah politik dunia.
한국어
통신 관련 문제에서 패권 정치가 배제될 수 있다는 생각은 낙관적일 뿐만 아니라 역사와도 맞지 않습니다. 이 보고서는 국가가 통신 안보에 안주하면 세계 정치의 판도가 바뀔 수 있음을 보여줍니다.
Srpsko-hrvatski
Ideja da se politika moći može ukloniti iz pitanja o telekomunikacijama nije samo optimistična, već nije u skladu s povijesti. Ovo izvješće pokazuje da kad su države nezainteresirane za svoju telekomunikacijsku sigurnost, rezultati mogu preoblikovati svjetsku politiku.
Preuzmite cjelovito izvješće (PDF) »
Español
La idea de que la política del poder se pueda excluir de las cuestiones de las telecomunicaciones no solo es optimista, sino también está desconectada de la historia. En este informe, se muestra que cuando los estados se conforman con la seguridad de sus telecomunicaciones, los resultados pueden reordenar la política mundial.
Descargar el informe completo (PDF) »
Türkçe
Güç diplomasisinin telekomünikasyonla ilgili konulardan ayrı tutulabileceği düşüncesi, yalnızca iyimser değil, aynı zamanda tarihle de bağdaşmıyor. Bu rapor, devletler telekomünikasyon güvenlikleri konusunda rehavete kapıldığında bunun sonuçlarının dünya siyasetini yeniden şekillendirebileceğini gösteriyor.
Tiếng Việt
Khái niệm về chính trị quyền lực có thể nằm ngoài những vấn đề viễn thông không chỉ lạc quan mà còn không tuân theo lịch ngành sử viễn thông. Báo cáo này cho thấy khi các nước tự mãn về an ninh viễn thông của mình thì kết quả có thể định hình lại chính trị thế giới.
Tải xuống báo cáo đầy đủ (PDF) »
This report was completed before Rush Doshi’s government service, involves only open sources, and does not necessarily reflect the official policy or position of any agency of the U.S. government.
-
Acknowledgements and disclosures
The authors wish to thank former interns Isabella Lu, Zijin Zhou, and Gaoqi Zhang for their research assistance on this project, several anonymous reviewers, Claire Harrison and Ted Reinert for editing the report, and Chris Krupinski and Rachel Slattery for layout and web design. Brookings is grateful to the U.S. Department of State and the Institute for War and Peace Reporting for funding this research.
-
Footnotes
- Steven Chase, Robert Fife, and Barrie McKenna, “Trudeau refuses to let ‘politics slip into’ decision on Huawei,” The Globe and Mail, October 15, 2018, https://www.theglobeandmail.com/politics/article-trudeau-refuses-to-let-politics-slip-into-decision-on-huawei/; Greg Quinn and Josh Wingrove, “Trudeau Says Politics Won’t Factor Into Huawei 5G Decision,” Time, December 19, 2018, https://time.com/5485141/justin-trudeau-huawei-5g-decision-politics/.