From smart cities, to smart cars, to smart factories, the future will be built on ubiquitous microchips connected by wireless networks. Fifth generation (5G) technology promises to bring the high-speed, low latency wireless infrastructure necessary for the “smart” era. Moving from promise to reality, however, will require those networks to be secure.
The introduction of 5G networks is both a response to the massive wave of digitization that is sweeping the economy as well as a stimulant to its further expansion. By some estimates, half of all worldwide data traffic over the next five years will be generated not by people, but by computerized devices requiring no human intervention.
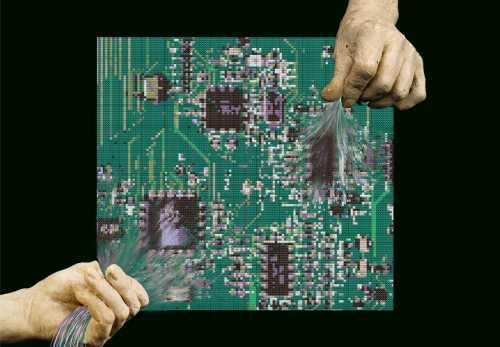
Fifth generation wireless networks will deliver amazing and important new capabilities and services. Yet, 5G also brings with it new cybersecurity challenges. Securing networks that utilize potentially insecure components while operating in an inherently insecure world is a new challenge. It is a problem that is expanded by how the exponential growth in data traffic threatens the efficacy of traditional traffic-based cybersecurity monitoring.
The purpose of this paper is not to criticize the amazing engineering that produced 5G, but to call attention to how these decisions, by introducing a new network architecture, have fallen short in affirmatively addressing avoidable cybersecurity risk while also introducing new cybersecurity concerns, and to suggest how those concerns might be mitigated by a combination of agile regulatory oversight, corporate focus, and government funding.
The Brookings Institution is committed to quality, independence, and impact.
We are supported by a diverse array of funders. In line with our values and policies, each Brookings publication represents the sole views of its author(s).