Over the last six years, nearly 1,500 breach incidents have potentially exposed the medical data of more than 155 million Americans, according to statistics reported by the Department of Health and Human Services’ Office for Civil Rights.
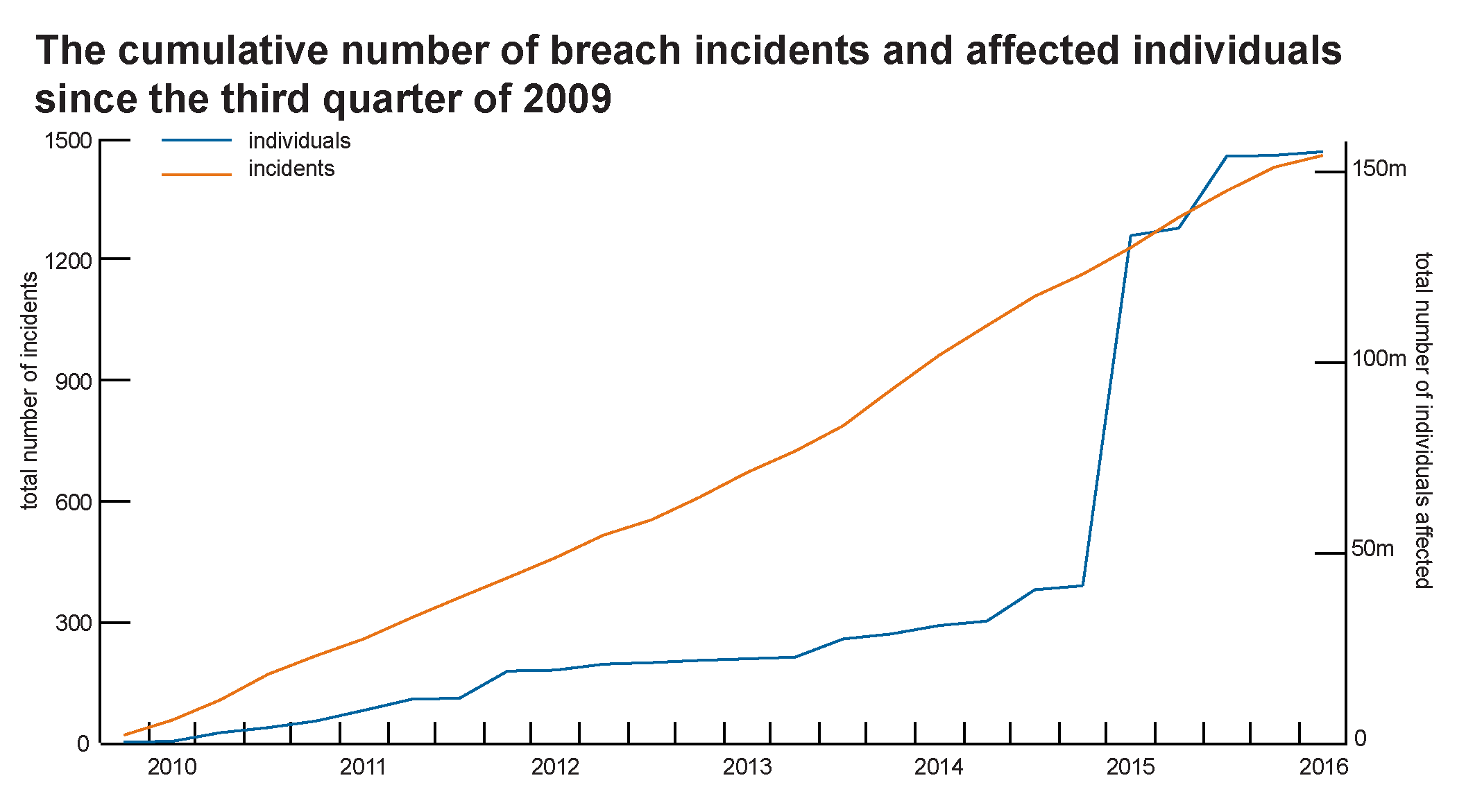
The frequency and magnitude of privacy breaches have trended upward in recent years. According to statistics from the Identity Theft Resource Center, data breaches are more likely to happen in the health care industry than any other sector. Experian predicts that this sector will continue to experience an increasing volume of hacking attacks in 2016.
On average, two breach incidents occur per 1,000 physicians. Privacy breaches occur most frequently in Maine, at four times more than the national average, while Wyoming and Montana rank second and third with breach incident rates at triple the national average.
Why do such incidents happen so frequently in the health care sector and how could they be prevented?
To answer these questions, I talked with key personnel at twenty-two different hospitals, insurers, and business associates that had experienced a breach incident over the last two years. A new report synthesizes the lessons learned from those incidents and highlights the unique vulnerabilities of the health care system to privacy breaches. The report lays out the following recommendations on how government action in the short run and a cyber-insurance market in the long run can provide a remedy for the current problem and ensure the privacy of patients:
Health care organizations should prioritize patient privacy and use available resources to protect it
In many of the interviewed organizations, privacy breaches could have been prevented had they spent enough on security technologies or diligently followed privacy policies. Health care organizations now have access to both the required knowledge and technology to ensure the privacy of their patients, and they should use these resources to their fullest potential.
Office for Civil Rights (OCR) should better communicate the details of its audits
After a breach occurs, OCR conducts a thorough investigation to identify the causes. Through these audits, OCR also confirms that the victim organization has enacted corrective and preventive policies to avoid second incidents. Although the lessons learned from each breach can prevent similar breaches, OCR does not share the details of its investigations. OCR should provide detailed reports on how each breach happened and how other health care organizations can avoid similar incidents.
Health care organizations should better communicate with each other
Health care organizations should share information about security technologies, privacy policies, and breach incidents with each other and with federal agencies. This information sharing should be incentivized, and health care organizations should be encouraged to use currently available platforms to better share information among themselves.
OCR should establish a universal HIPAA certification system
OCR should prevent much more than it punishes, and their random audits are effective in preventing initial breaches. OCR should accredit certification agencies that can conduct preventive audits in accordance with OCR standards and certify organizations that comply with the Health Insurance Portability and Accountability Act.
The health care sector should embrace cyber insurance
In the long run, a cyber insurance market can fundamentally improve how patient privacy is viewed and managed in the health care sector. To underwrite the privacy risk of health care organizations, cyber insurance companies will conduct timely and efficient audits and proactively manage their clients’ privacy protection efforts. Health care organizations will also have a direct economic incentive to reduce their cyber insurance premiums by addressing their security weaknesses and preventive privacy breaches.
You can read the full report here.

Commentary
Patient privacy: Can past lessons prevent future failures?
May 5, 2016