On December 4, the Center for East Asia Policy Studies at Brookings hosted its second Asia Transnational Threats Forum (ATTF) on counterterrorism in Asia. Following the first ATTF conference on Asia cybersecurity in June, the second forum explored how the threat of terrorism is evolving in the region and how East Asian countries are approaching counterterrorism through their national policies and through regional and international cooperation.
The 2018 Winter Olympics in Pyeongchang, South Korea and the upcoming Olympics in Tokyo in 2020 and Beijing in 2022 will put a spotlight on this issue, especially given the increase of terror incidents in the region. More importantly, Asia’s economic wealth, growing regional connectivity, importance in the global economy, and status as a driver in developing and using emerging technologies have important implications for how individual states and the global community counter violent extremism and deter homegrown threats.
To host the winter Olympics in Pyeongchang, South Korea undertook its largest-ever foreign intelligence cooperation operation. Through the technical assistance of the FBI, CIA, and other foreign partners—encompassing 34 countries and 52 intelligence agencies in total—South Korean authorities were able to share and access updated information on potential suspects, according to Director Yeong Gi Mun, South Korea’s chief of the Counterterrorism Center. This global collaboration involved sharing best practices on analytic tools and techniques to identify vulnerabilities. The effort was also aided by the use of technology, particularly intelligent closed-circuit TVs (CCTVs) and facial recognition devices. Although Mun considered the international effort during the Olympics a success, highlighting in particular the importance of timely intelligence sharing, he also shared key lessons and challenges. These include the need to build in enough time prior to the event to account for unpredictable weather and equipment malfunctions, educate and train volunteers, check venues, and rehearse plans.
Looking at future terrorism-related challenges for South Korea and the region more broadly, Mun emphasized the significant threat posed by terrorists’ increased use of cyberspace and advanced technology, a theme that other expert panelists raised as well. As the first ATTF conference highlighted, the anonymity and ubiquity of the cyber realm provides actors an attractive, low-cost method to wreak havoc on a mass scale. Moreover, growing regional connectivity has allowed for the spread of extremist propaganda via the internet and social media, attracting individuals who might be convinced to conduct lone wolf attacks or other violent acts.
While the threat of returning foreign fighters is relatively low in South Korea, Ji-Hyang Jang of the Asan Institute for Policy Studies argued that extremist views disseminated in South Korea are not tied to any particular religion or race, but are more related to frustrations stemming from social and economic inequality. Audrey Cronin of American University explained that the sharp increase in the wealth gap in East Asia in recent decades—with its attendant urban-rural divide and disparities in access to education, healthcare, and prosperity—can help militant groups exploit these conditions to recruit disaffected individuals, especially youth, through technological means. Hori Mayuko of Japan’s Ministry of Foreign Affairs also stressed the concern over homegrown terrorism in Japan and raised a recent incident where a university student in Nagoya was arrested for producing materials for an improved explosive device (IED) with ingredients and methods that were easily accessible online.
The university student in Nagoya also possessed a gun made by a 3D printer, highlighting concerns with dual-use technologies. Cronin observed how violent actors are combining technologies to weaponize devices like drones and 3D printers. There are currently no effective countermeasures to deal with this combination, which will have greater consequences when applied to the wider Internet of Things (including electronic appliances and devices that have sensor technology). Attacks combining technologies in this way will be especially difficult to counter, Cronin warned, since “we do not have the institutional structures and commercial incentives to prepare for these looming threats.”
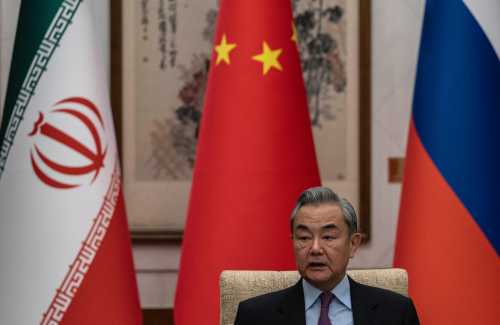
States in Asia are using their own legal and technological means fight terrorism. In the case of China, which does not have an official definition of terrorism, Samm Sacks of New America Foundation noted that counterterrorism laws have allowed for greater government control and visibility into the internet, with telecom and internet service providers assisting the state in monitoring extremist content online. But in a disturbing development, the Chinese government has been testing the application of technology in Xinjiang to monitor the activities of the minority Uighur Muslim population. This includes technology for facial recognition, voice data collection, and separate QR codes for each household that allow authorities to view their online data and networks. While many already assume that this type of technology is being applied outside of Xinjiang, Sacks clarified that this is actually not the case, since there are technical limits of sharing data. Interestingly enough, she explained that the perception of surveillance itself has become a key deterrent to illegal activities in China.
James Baker, former general counsel of the FBI, and currently a Visiting Fellow in the Brookings Governance Program, outlined the four “must-haves” for implementing an effective counterterrorism policy under the rule of law.
First, he called for effective management of counterterrorism agencies through clear goals and accountability. In the case of South Korea, Jang described interagency friction amongst the five government agencies dealing with countering violent extremism. This has led to a lack of coherent policy, giving rise to disagreements about South Korea’s participation in global cooperation efforts for fears of attracting attention from groups like the Islamic State.
Baker also stressed the need for clear laws regarding intelligence collection and dissemination. Despite Indonesia’s tremendous progress in terms of defending the rule of law and democracy, Zachary Abuza of the National War College pointed out some troubling aspects of their new counterterrorism law, which allows for the stripping of citizenship and increased use of preventative detention.
Lastly, counterterrorism policy must be implemented with the right people with right values (internal controls), as well as outside oversight (external controls). Through assistance from the United States, Australia, and Japan, Indonesia developed an elite, independent counterterrorism police unit in 2002 that was separate from the country’s military. But Abuza pointed out that Indonesia’s new counterterrorism law has granted greater authority to Indonesian military forces, who have been trying to regain some of their political and economic powers they have lost since 1998. A formal counterterrorism rule for the military plays into jihadists’ narrative that the state is oppressive and anti-Islamic. Externally, countries like the United States, Singapore, and Australia have been providing financial assistance to the military in the Philippines for their counterterrorism efforts, but Abuza urged the need for greater accountability and benchmarks from assistance-providers to avoid creating moral hazards.
In the East Asia Pacific—a highly diverse region located at the intersection of growing economic prosperity, technological advances, and connectivity—Baker’s four “must-haves” for effective counterterrorism policies offer useful guideposts for domestic measures and regional and global collaboration. As the panelists highlighted, however, these same characteristics can continue be drive terrorism in Asia, suggesting the importance of ensuring ongoing communication, collaboration, and capacity-building to combat the terrorism threat.
The Brookings Institution is committed to quality, independence, and impact.
We are supported by a diverse array of funders. In line with our values and policies, each Brookings publication represents the sole views of its author(s).








Commentary
Experts discuss terrorist threats facing Asia, and ways forward
December 21, 2018