Executive Summary:
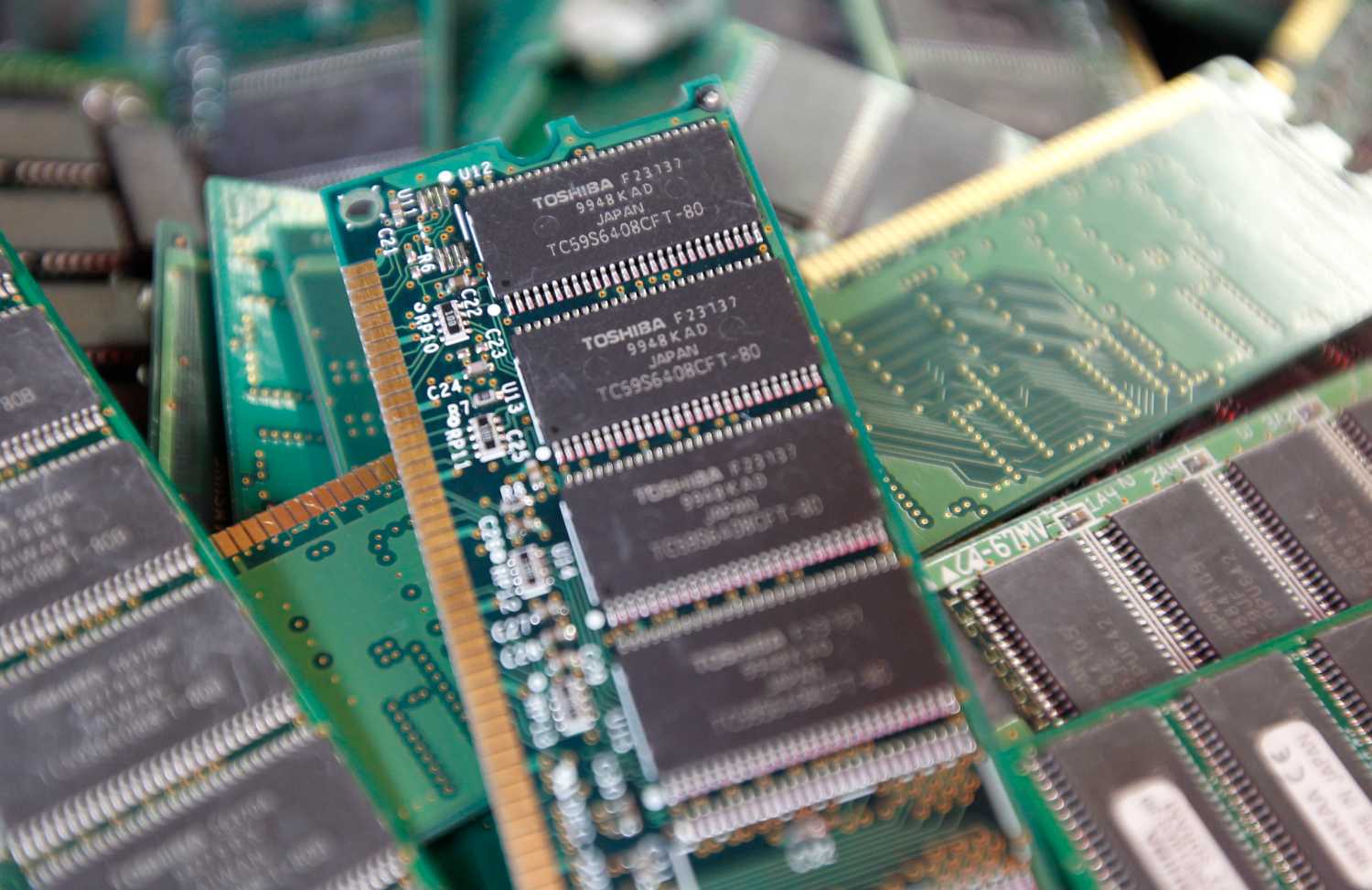
Electronic “chips” are found everywhere—not just in critical defense systems, but also in the broader infrastructure for power, finance, communications, and transportation. All of these systems function effectively only when the electronic circuits at their heart can be trusted to operate as intended.
Unfortunately, ensuring trust has become much more difficult in recent years. Concern over the growth of counterfeit electronics (parts that have been harvested from discarded systems, relabeled, and sold as new to unsuspecting buyers) has grown in recent years. These parts can fail prematurely, with potentially disastrous consequences. Thanks to recent congressional attention, improved detection methods, and heightened screening requirements for parts destined for defense systems, however, the threat of counterfeits is being actively addressed.
Yet the supply chain is almost completely unprotected against a threat that may turn out to be more significant in the long term: Chips could be intentionally compromised during the design process, before they are even manufactured. If placed into the design with sufficient skill, these built-in vulnerabilities would be extremely difficult to detect during testing. And, they could be exploited months or years later to disrupt—or exfiltrate data from—a system containing the compromised chip.
As chips have gotten more complex and design teams have grown larger and more globalized, the opportunities to insert hidden malicious functionality have increased. If the history of cybersecurity has taught us anything, it is that these opportunities will be exploited. The prudent question, therefore, is not “will intentionally compromised hardware end up in the defense electronics supply chain?” but “how do we maintain security when it inevitably does?” This paper aims to help frame the discussion regarding how best to respond to this important and underappreciated aspect of cybersecurity.
The Brookings Institution is committed to quality, independence, and impact.
We are supported by a diverse array of funders. In line with our values and policies, each Brookings publication represents the sole views of its author(s).